Prowler authenticates to Okta as a service application using OAuth 2.0 with a private-key JWT (Client Credentials grant). The integration is read-only by scope and follows DISA STIG guidance for least-privilege access.Documentation Index
Fetch the complete documentation index at: https://docs.prowler.com/llms.txt
Use this file to discover all available pages before exploring further.
Common Setup
Prerequisites
- An Okta organization. The UI examples below use Identity Engine terminology such as Global Session Policy; Classic Engine exposes equivalent sign-on policy concepts under older naming.
- A Super Administrator account on that organization for the one-time service-app setup.
- An API Services app integration created in the Okta Admin Console.
Authentication Method Overview
| Method | Status | Use Case |
|---|---|---|
| OAuth 2.0 (private-key JWT) | Supported | Production scans, CI/CD, Prowler App. |
If a different authentication method is needed (SSWS API token, OAuth with user delegation, etc.), please open a feature request describing the use case.
Required OAuth Scopes
The bundled checks require the following read-only scopes:okta.policies.readokta.brands.readokta.apps.read
| Scope | Used by |
|---|---|
okta.policies.read | Sign-on, password, and authentication policies |
okta.brands.read | Sign-in page customizations (DOD Notice and Consent Banner check) |
okta.apps.read | First-party app settings (Okta Admin Console session), integrated app inventory, and the Authentication Policies bound to Okta applications |
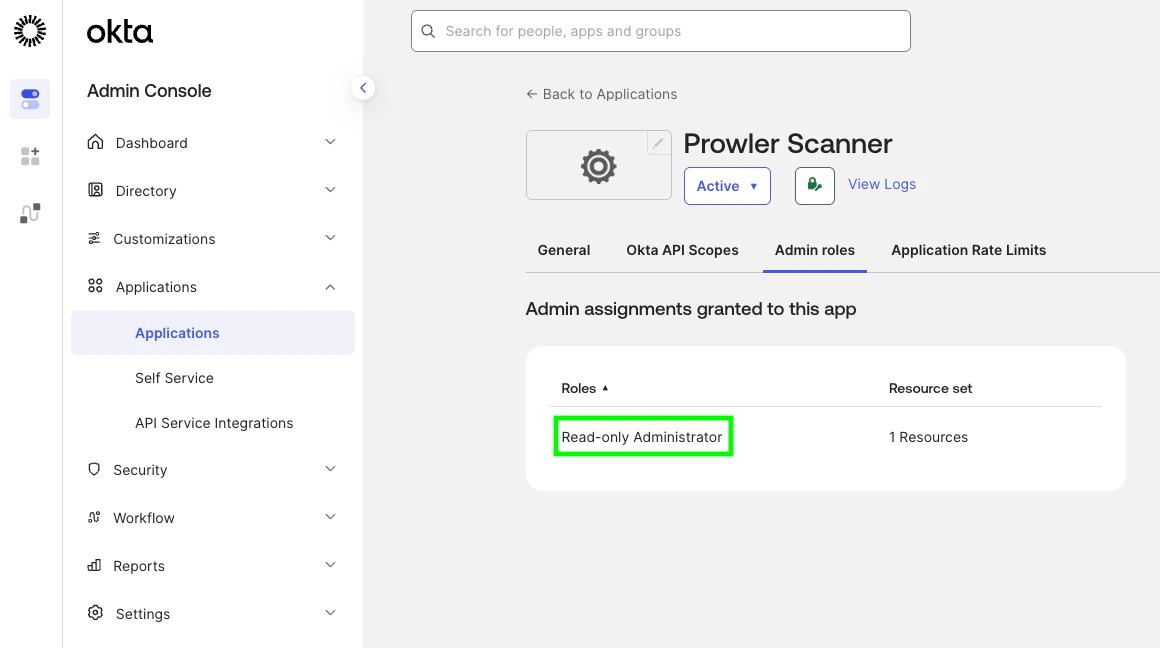
Required Admin Role
The service application must be assigned one of the following Okta admin roles:- Read-Only Administrator — covers every
signoncheck and runsapplication_authentication_policy_network_zone_enforcedagainst the apps it can see. Visibility caveat: under Read-Only Administrator the/api/v1/appsendpoint returns only the apps the service application is itself assigned to — typically just the service app’s own row (for example,Prowler Scanner). The check still produces a finding for that app, but the rest of the org’s app inventory is invisible at this role level. - Super Administrator — required additionally to evaluate five application-service checks that target Okta’s first-party apps (Okta Admin Console, Okta Dashboard). With Super Administrator,
application_authentication_policy_network_zone_enforcedalso evaluates the full org-wide app inventory instead of the service-app-only slice.
403 Forbidden. Read-Only Administrator is the minimum role that lets the granted okta.*.read scopes return configuration data to Prowler’s checks; without it, the credential probe at provider startup fails and the scan never gets to evaluate any check.
When Super Administrator is required
Four checks need to resolve the Authentication Policy bound to Okta’s first-party apps (Okta Admin Console, Okta Dashboard) and depend on/api/v1/apps returning those system apps — which Okta restricts to Super Administrator:
| Check | STIG |
|---|---|
application_admin_console_mfa_required | V-273193 |
application_admin_console_phishing_resistant_authentication | V-273191 |
application_dashboard_mfa_required | V-273194 |
application_dashboard_phishing_resistant_authentication | V-273190 |
saasure, okta_enduser) out of /api/v1/apps for every role below Super Administrator, so okta.apps.read alone is not enough. The okta.apps.manageFirstPartyApps permission exists only in the paid Okta Identity Governance role ACCESS_REQUESTS_ADMIN and cannot be added to custom roles (Okta Permissions Catalog).
A fifth check — application_admin_console_session_idle_timeout_15min (STIG V-273187) — also requires Super Administrator: it calls GET /api/v1/first-party-app-settings/admin-console, which returns 403 E0000006 for every role below Super Administrator.
When the service app runs with Read-Only Administrator, the five checks listed in this section return MANUAL instead of PASS/FAIL — the rest of the scan keeps running.
Read-Only Administrator stays the recommended default for the least-privilege framing that aligns with DISA STIG. Assign Super Administrator on a separate run when full coverage of the first-party app checks is needed.
Step-by-Step Setup
1. Go to the admin console
2. [Optional] - Disable the privilege-escalation bypass (org-wide, one-time)
In the Okta Admin Console, go to Settings → Account → Public client app admins and ensure it is off. When enabled, every API Services app can be auto-assigned the Super Administrator role after scopes are granted, which would invalidate the read-only premise of this integration.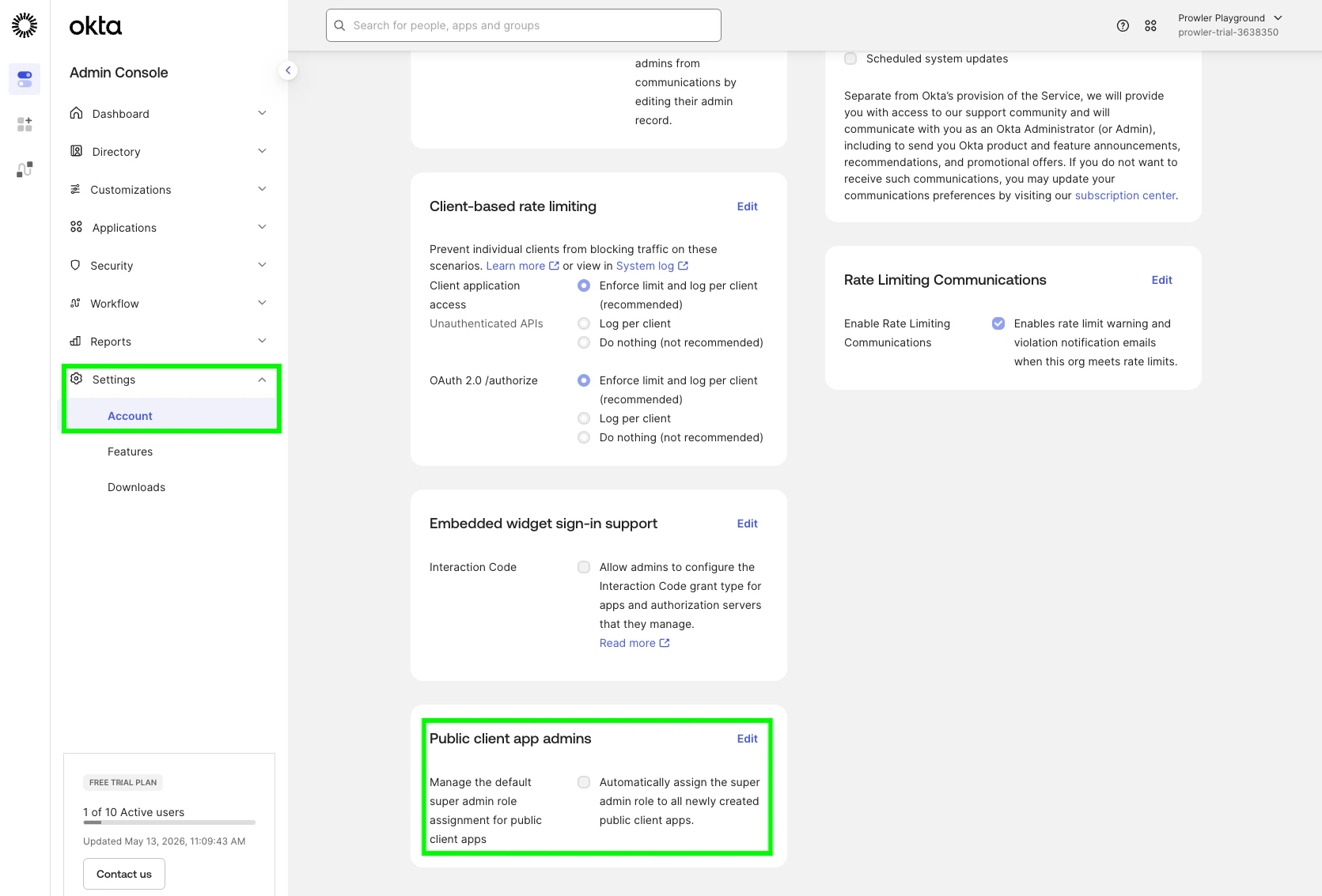
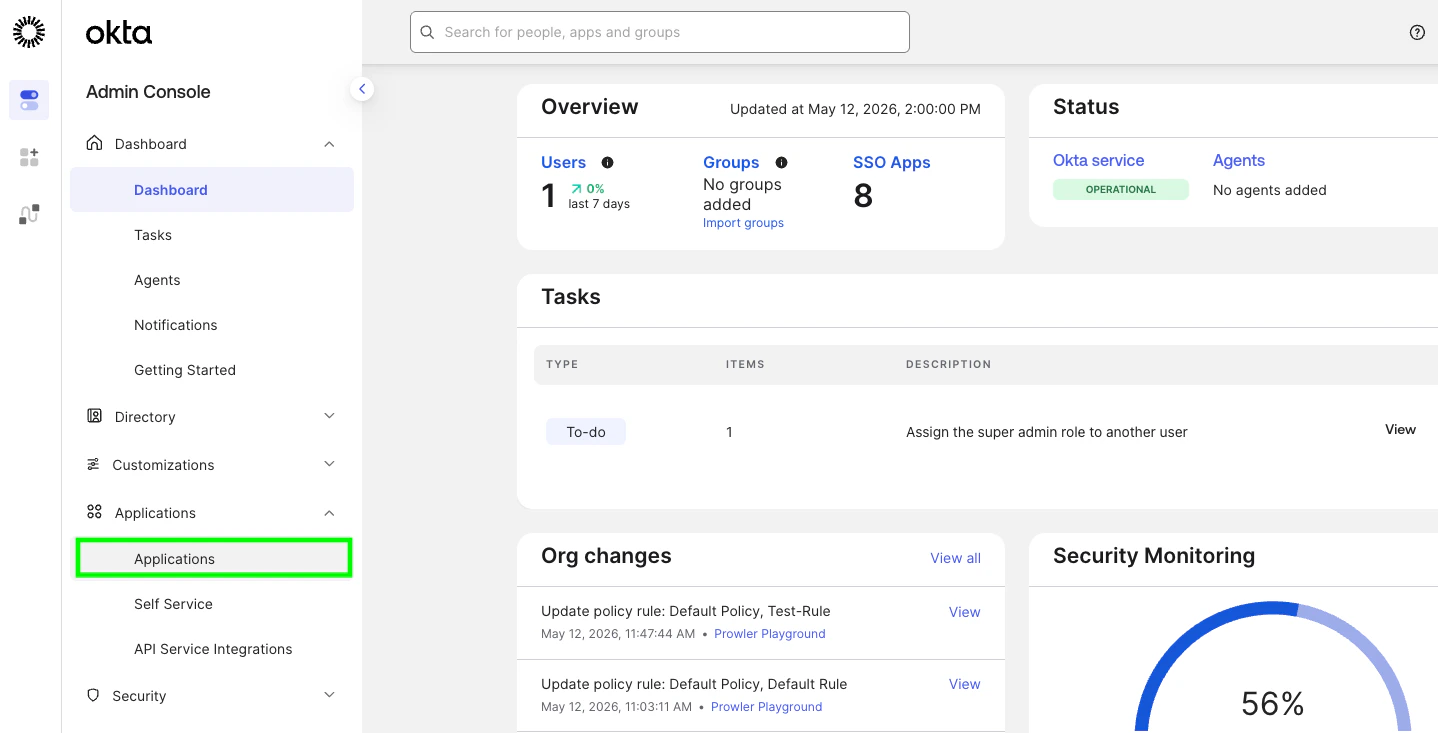
3. Create the API Services app
- Go to Applications → Applications.
- Create App Integration
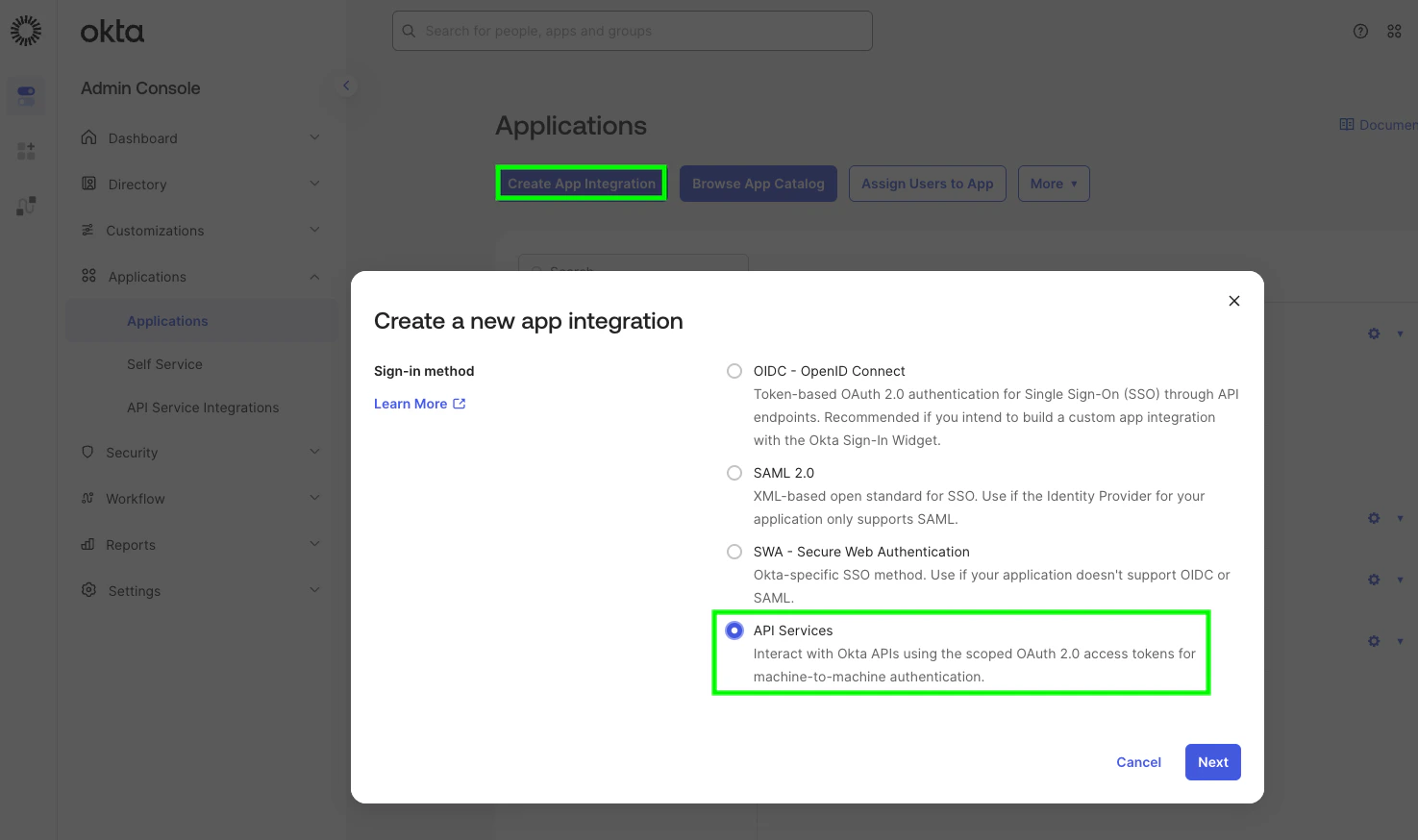
- Sign-in method: API Services. Click Next.
- Name the app (for example,
Prowler Scanner) and click Save. - Copy the displayed Client ID — you’ll use it as
OKTA_CLIENT_ID.
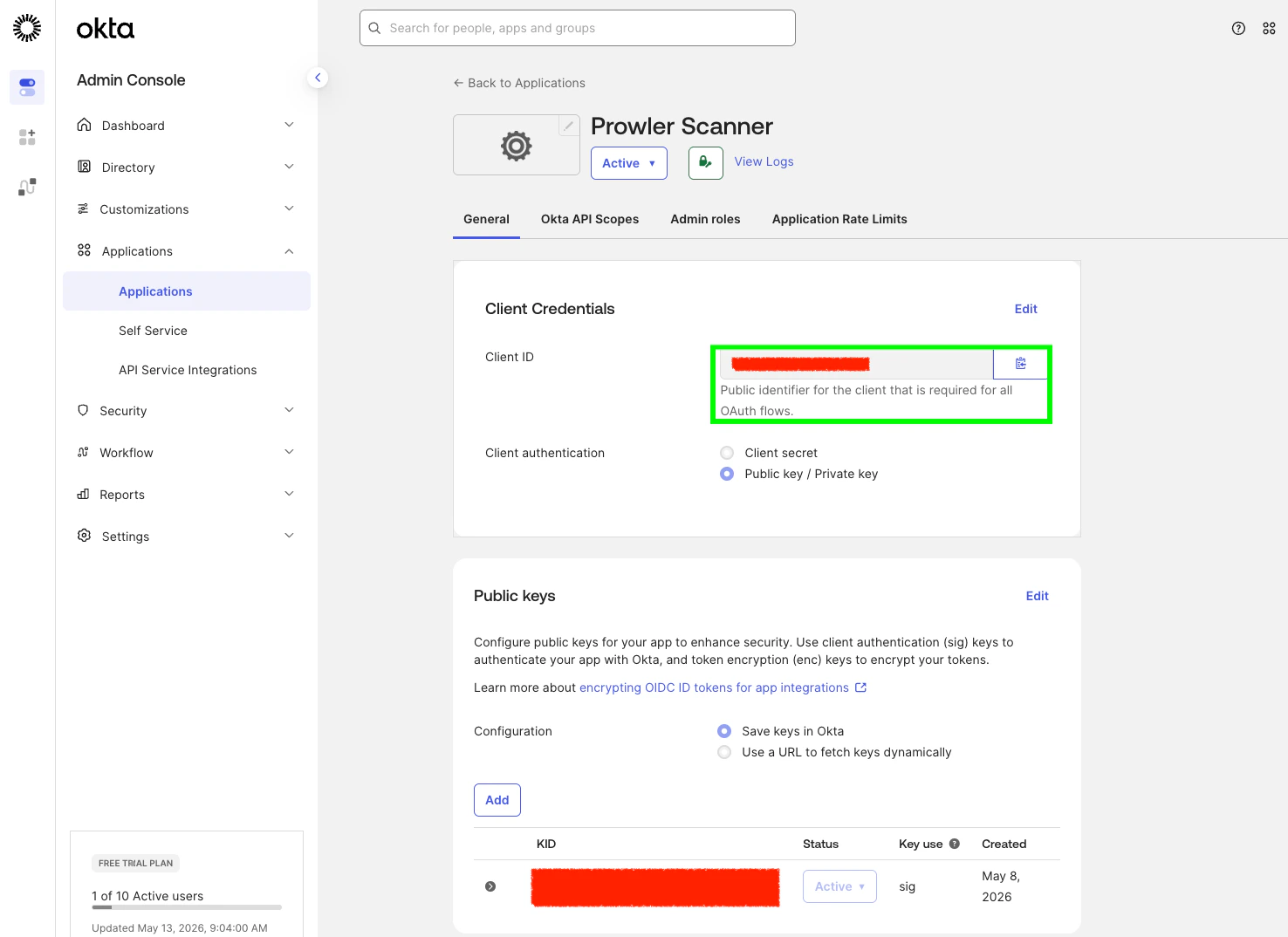
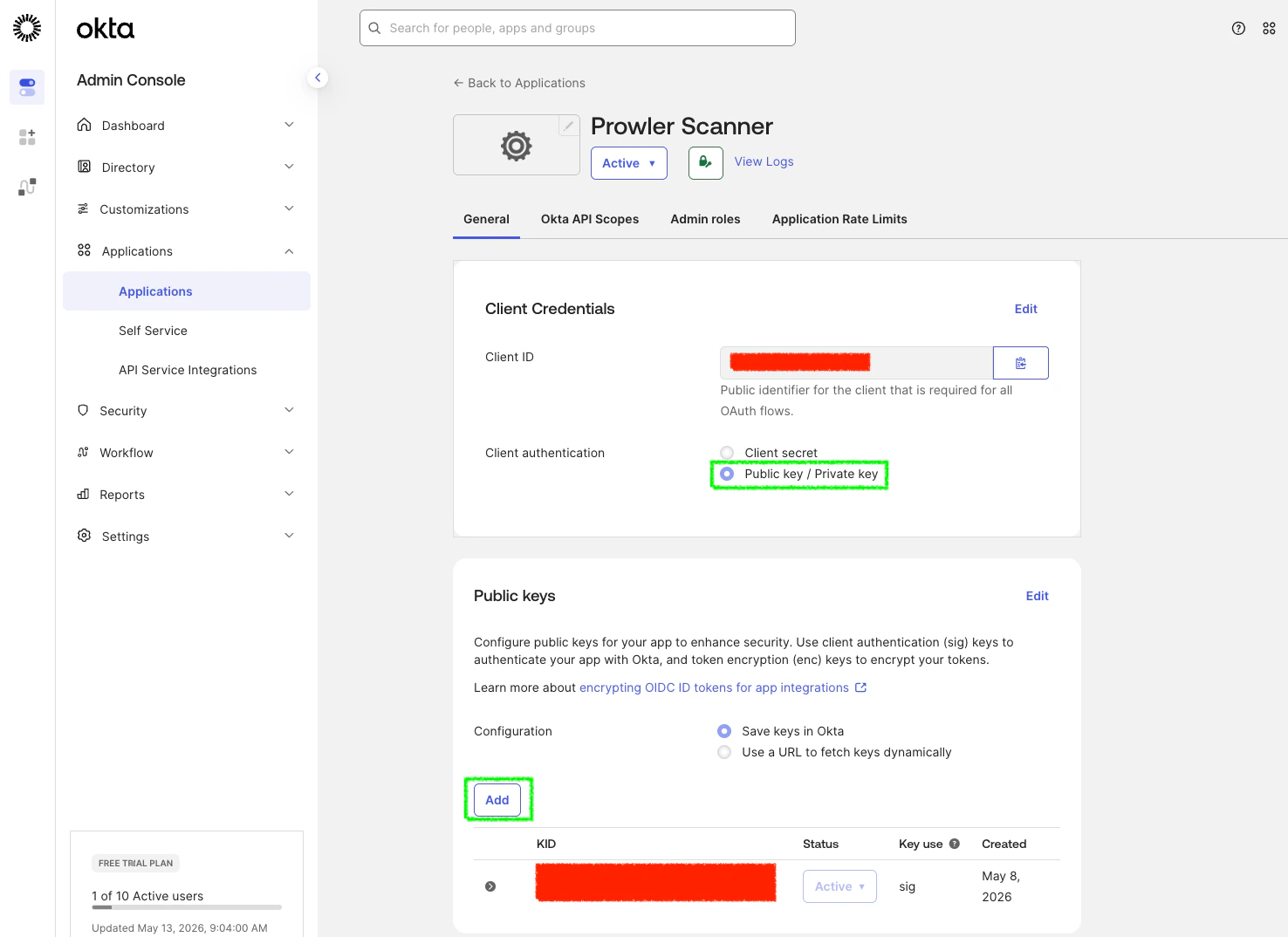
4. Switch to private-key authentication and generate a keypair
On the new app’s General tab, scroll to Client Credentials:- Click Edit.
- Set Client authentication to Public key / Private key.
- Under Public Keys, click Add key.
- In the modal, click Generate new key. Okta creates a JWK pair.
- Click the PEM tab to switch the displayed format (or keep JWK — Prowler accepts both).
- Copy the entire
-----BEGIN PRIVATE KEY-----block (or the JWK JSON). - Click Done, then Save.
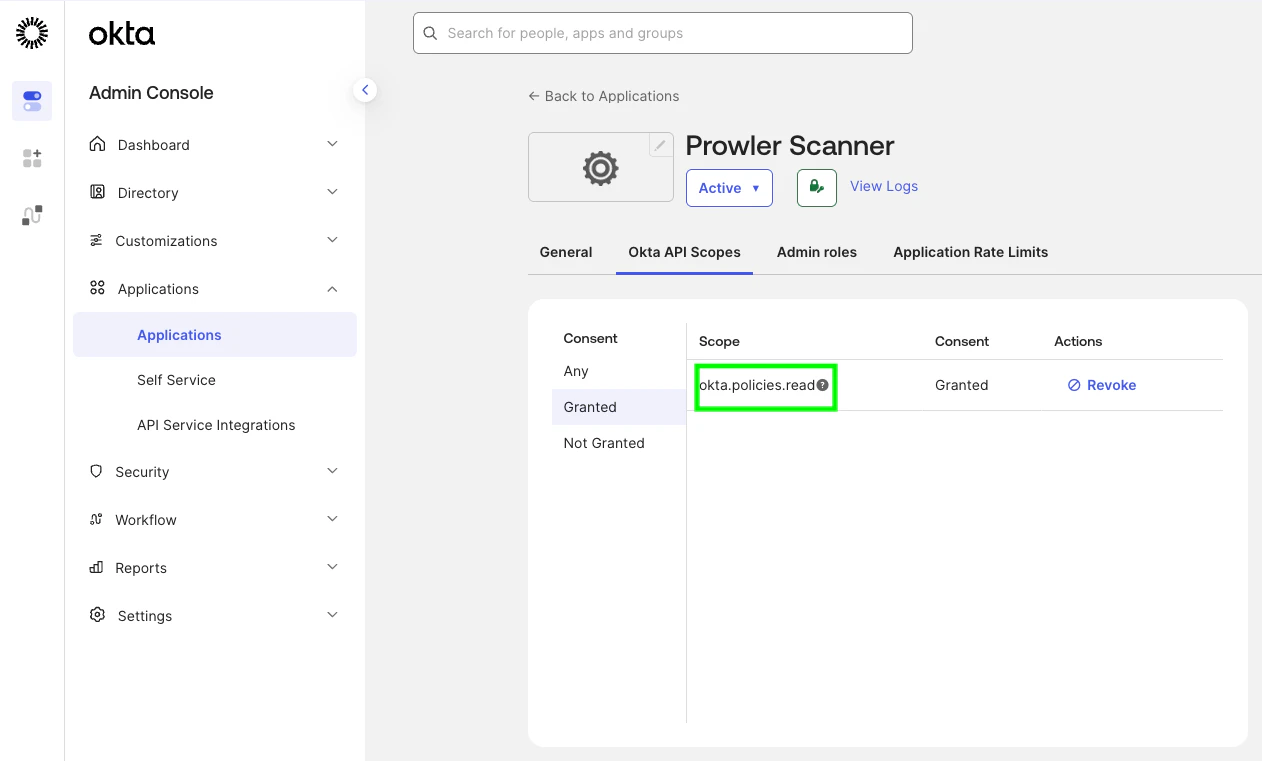
5. Grant the required OAuth scopes
On the app, open the Okta API Scopes tab and click Grant on every scope Prowler needs. The bundled checks requireokta.policies.read, okta.brands.read, and okta.apps.read.
6. Assign an admin role
On the app, open the Admin roles tab and click Edit assignments → Add assignment:- Role: Read-Only Administrator (default) — covers every
signoncheck and runs the per-app network-zone check against the apps the service app can see (typically only the service app’s own row). - Resources: All resources
7. [Optional] Verify DPoP setting
Prowler sends DPoP (Demonstrating Proof of Possession) proofs on every token request. The integration works whether the Require Demonstrating Proof of Possession (DPoP) header in token requests setting on the service app is on or off — but enabling it is the more secure default.Prowler CLI Authentication
Using Environment Variables (Required for Secrets)
Private key material must be supplied via environment variables — Prowler does not accept secrets through CLI flags.Non-Secret CLI Flags
Non-secret values are also available as CLI flags for ergonomic overrides:| Flag | Equivalent env var |
|---|---|
--okta-org-domain | OKTA_ORG_DOMAIN |
--okta-client-id | OKTA_CLIENT_ID |
--okta-scopes | OKTA_SCOPES |
Troubleshooting
OktaInvalidOrgDomainError
The org domain must be <org>.okta.com (or .oktapreview.com / .okta-emea.com / .okta-gov.com / .okta.mil / .okta-miltest.com / .trex-govcloud.com). Pass the bare hostname only — no https:// scheme, no path, no trailing slash. Custom (vanity) domains are not currently accepted.
OktaPrivateKeyFileError
The file at OKTA_PRIVATE_KEY_FILE is missing, unreadable, or empty. Confirm the path and that the file contains a non-empty PEM block or JWK JSON document.
OktaInvalidCredentialsError at provider init
Prowler validates credentials at startup by listing one sign-on policy. This error indicates the credential material itself was rejected:
invalid_client— the public key registered in Okta does not match the private key on disk. Generate a fresh keypair and try again.
OktaInsufficientPermissionsError at provider init
Raised when the credential probe succeeds at the OAuth layer but the request is rejected because the service app lacks the required scope or admin role:
invalid_scope— one of the requested scopes (okta.policies.read,okta.brands.read, orokta.apps.read) is not granted on the service app. Grant the missing scope from Okta API Scopes.Forbidden/not authorized— no admin role is assigned to the service app. Assign Read-Only Administrator (or Super Administrator for the first-party application checks) from Admin roles.
Application-service checks return MANUAL on first-party apps
When the service app runs with Read-Only Administrator, the five application-service checks targeting the Okta Admin Console and Okta Dashboard return MANUAL. This is by design — Okta restricts the underlying endpoints (/api/v1/first-party-app-settings/{appName} and /api/v1/apps for first-party app name values saasure / okta_enduser) to Super Administrator. Assign the Super Administrator role to the service app to evaluate those checks. See Required Admin Role for the full list.