The official Prowler GitHub Action runs Prowler scans inside your GitHub workflows using the officialDocumentation Index
Fetch the complete documentation index at: https://docs.prowler.com/llms.txt
Use this file to discover all available pages before exploring further.
prowlercloud/prowler Docker image. It supports every Prowler provider (AWS, Azure, GCP, Kubernetes, GitHub, Cloudflare, IaC, and more), optionally pushes findings to Prowler Cloud, and uploads SARIF results to GitHub Code Scanning so findings appear in the Security tab and as inline PR annotations.
Source: prowler-cloud/prowler · Marketplace listing: Prowler Security Scan.
Inputs
| Input | Required | Default | Description |
|---|---|---|---|
provider | yes | — | Cloud provider to scan (aws, azure, gcp, github, kubernetes, iac, cloudflare, etc.) |
image-tag | no | stable | Docker image tag — stable (latest release), latest (master, not stable), or <x.y.z> (pinned). See available tags. |
output-formats | no | json-ocsf | Output format(s) for scan results. Space-separated (e.g. sarif json-ocsf) |
push-to-cloud | no | false | Push findings to Prowler Cloud. When true, PROWLER_CLOUD_API_KEY is auto-forwarded |
flags | no | "" | Additional CLI flags (e.g. --severity critical high). Values with spaces can be quoted: --resource-tag 'Environment=My Server' |
extra-env | no | "" | Space-, newline-, or comma-separated list of env var names to forward to the container (see Authentication) |
upload-sarif | no | false | Upload SARIF results to GitHub Code Scanning |
sarif-file | no | "" | Path to SARIF file (auto-detected from output/ if not set) |
sarif-category | no | prowler | Category for the SARIF upload (distinguishes multiple analyses) |
fail-on-findings | no | false | Fail the workflow step when findings are detected (exit code 3) |
Usage
AWS scan
Push findings to Prowler Cloud
Send scan results directly to Prowler Cloud for centralized visibility, compliance tracking, and team collaboration.When
push-to-cloud: true, PROWLER_CLOUD_API_KEY is forwarded automatically — set it in env: but don’t list it in extra-env. Requires a Prowler Cloud subscription and an API key with the Manage Ingestions permission. See API Keys.Upload SARIF to GitHub Code Scanning
Findings appear in the Security tab and as inline PR annotations when SARIF upload is enabled.Combine push-to-cloud with SARIF upload
Scan the current repository with the GitHub provider
--repository scans a single repo. Use --organization <name> instead to include org-level checks (MFA, security policies, etc.). See the GitHub provider authentication for required token permissions.Fail the PR on findings
By default the action tolerates findings (exit code 3) and succeeds. Setfail-on-findings: true to fail the workflow step when Prowler detects findings. Combine with --severity to control which severity levels trigger the failure:
if: always()) so findings appear in the Security tab regardless.
Authentication
Each provider requires its own credentials passed as environment variables. Credentials are not forwarded automatically — list every env var name you need in theextra-env input, and set its value via env: at the step, job, or workflow level (typically from secrets.*).
Refer to the Prowler provider docs for the full list of variables each provider supports. Common ones:
| Provider | Typical extra-env |
|---|---|
| AWS | AWS_ACCESS_KEY_ID AWS_SECRET_ACCESS_KEY AWS_SESSION_TOKEN AWS_DEFAULT_REGION (OIDC exports these automatically) |
| Azure | AZURE_CLIENT_ID AZURE_CLIENT_SECRET AZURE_TENANT_ID |
| GCP | GOOGLE_APPLICATION_CREDENTIALS CLOUDSDK_AUTH_ACCESS_TOKEN GOOGLE_CLOUD_PROJECT |
| GitHub | GITHUB_PERSONAL_ACCESS_TOKEN (or GITHUB_OAUTH_APP_TOKEN, or GITHUB_APP_ID GITHUB_APP_KEY) |
| Kubernetes | KUBECONFIG |
| Cloudflare | CLOUDFLARE_API_TOKEN (or CLOUDFLARE_API_KEY CLOUDFLARE_API_EMAIL) |
PROWLER_CLOUD_API_KEY is auto-forwarded when push-to-cloud: true — no need to add it to extra-env.AWS
Use aws-actions/configure-aws-credentials with OIDC (recommended) or pass static credentials. OIDC setsAWS_* env vars on the runner, so you only forward them:
Azure
Use azure/login with a service principal or pass credentials directly:GCP
Use google-github-actions/auth with Workload Identity Federation (recommended):Cloudflare
Create a Cloudflare API Token withZone:Read, Zone Settings:Read, and DNS:Read permissions (provider auth docs). Then:
Outputs
Scan results are written tooutput/ in the workspace and uploaded as artifacts named prowler-<provider> with 30-day retention.
When upload-sarif is enabled, SARIF results are also uploaded to GitHub Code Scanning and appear on the repository’s Security → Code scanning tab, filtered by the branch that ran the scan.
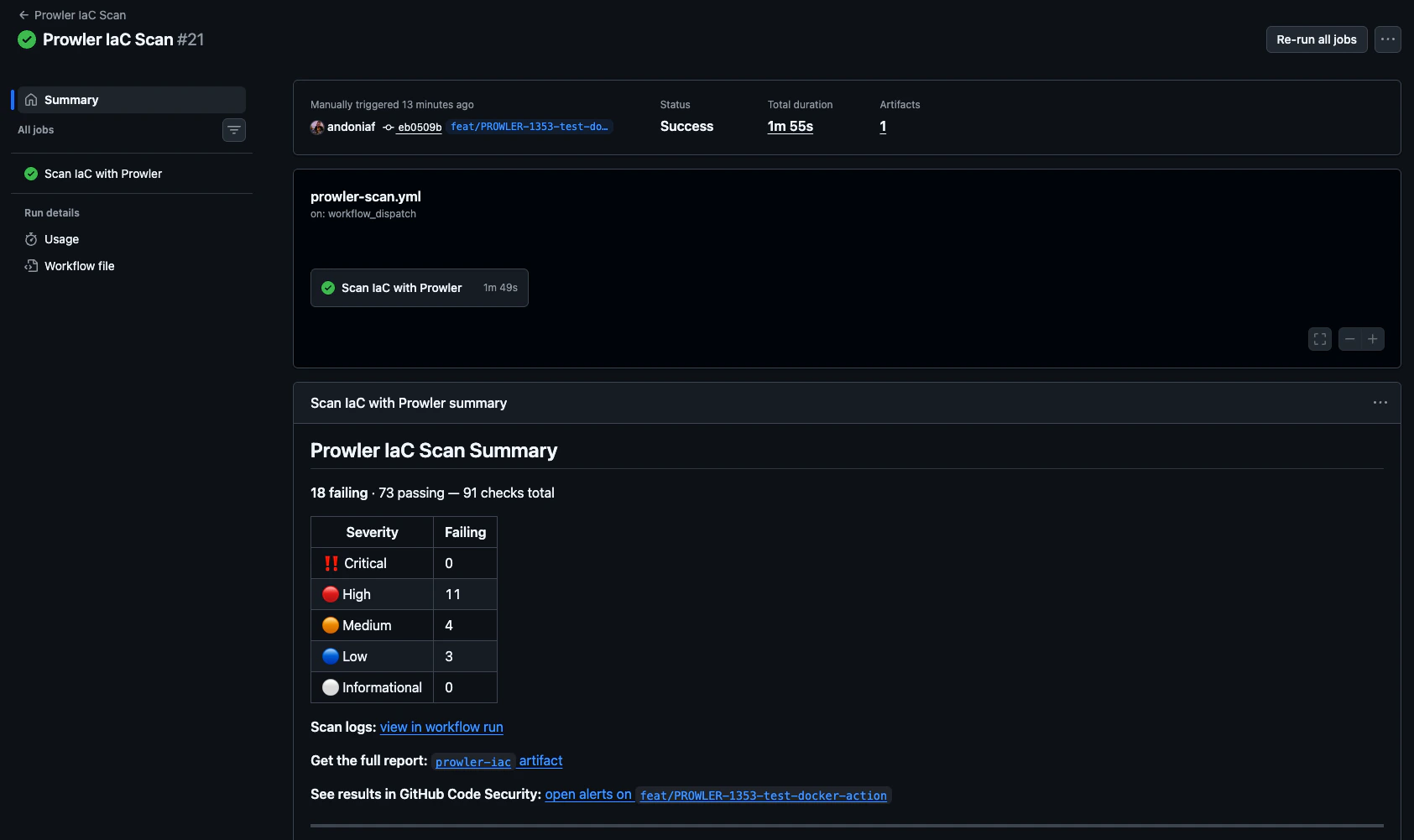
Step summary
The action writes a summary to the run page with a per-severity breakdown of failing checks, artifact and Code Scanning links, and (whenpush-to-cloud: false) a pointer to Prowler Cloud for continuous monitoring.