What is Prowler?
Prowler is the world’s most widely used open-source cloud security platform that automates security and compliance across any cloud environment. With hundreds of ready-to-use security checks, remediation guidance, and compliance frameworks, Prowler delivers AI-driven, customizable, and easy-to-use monitoring and integrations, making cloud security simple, scalable, and cost-effective for organizations of any size.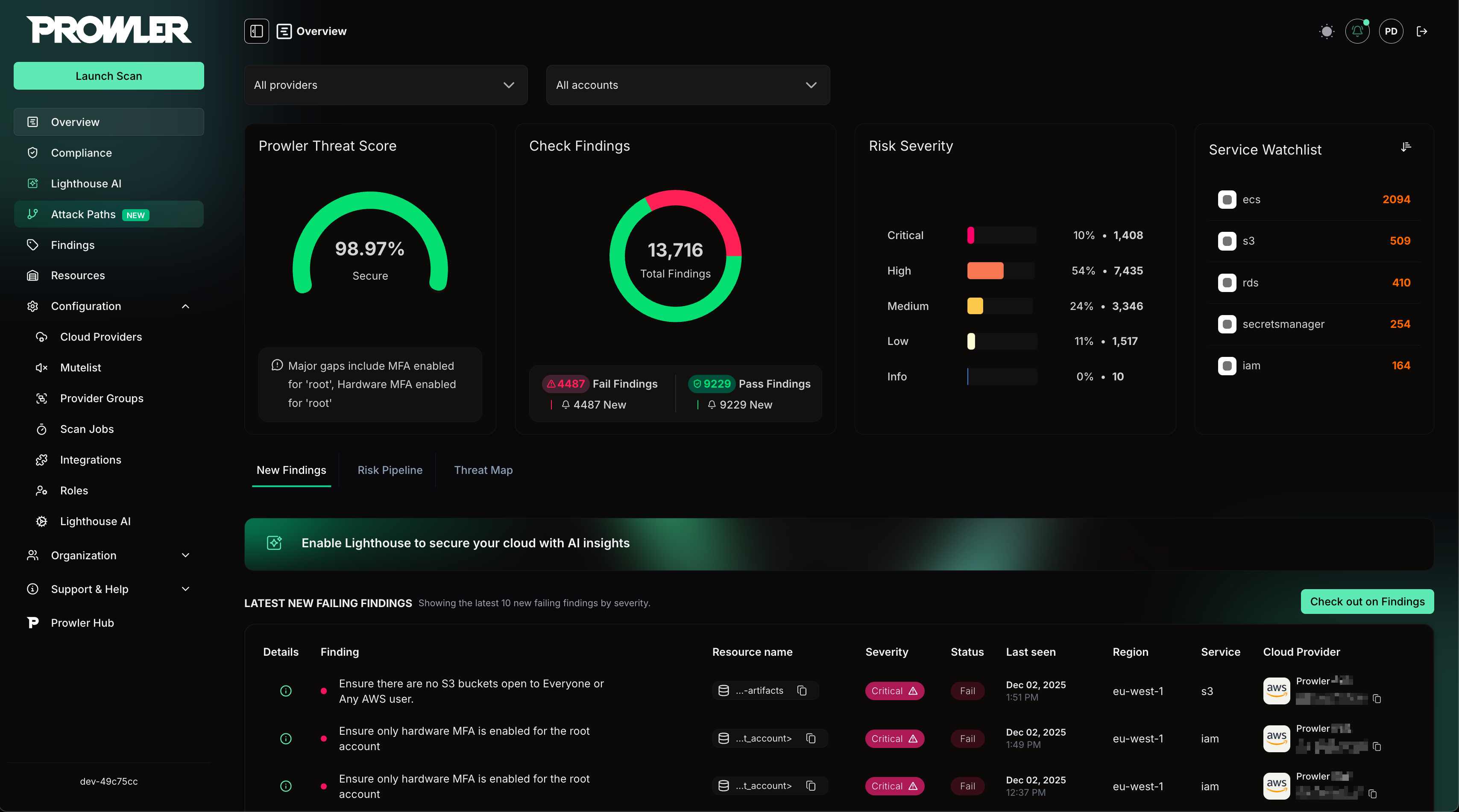
Prowler CLI
Command Line Interface
Prowler App
Web Application
Prowler Cloud
A managed service built on top of Prowler App.
Prowler Hub
A public library of versioned checks, cloud service artifacts, and compliance frameworks.
Supported Providers
Prowler supports a wide range of providers organized by category:Cloud Service Providers (Infrastructure)
| Provider | Support | Audit Scope/Entities | Interface |
|---|---|---|---|
| Alibaba Cloud | Official | Accounts | UI, API, CLI |
| AWS | Official | Accounts | UI, API, CLI |
| Azure | Official | Subscriptions | UI, API, CLI |
| Cloudflare | Official | Accounts | UI, API, CLI |
| Google Cloud | Official | Projects | UI, API, CLI |
| NHN | Contact us | Tenants | CLI |
| OpenStack | Official | Projects | UI, API, CLI |
| Oracle Cloud | Official | Tenancies / Compartments | UI, API, CLI |
| Scaleway | Contact us | Organizations | CLI |
| StackIT | Contact us | Projects | CLI |
Infrastructure as Code Providers
| Provider | Support | Audit Scope/Entities | Interface |
|---|---|---|---|
| Infra as Code | Official | Repositories | UI, API, CLI |
Software as a Service (SaaS) Providers
| Provider | Support | Audit Scope/Entities | Interface |
|---|---|---|---|
| GitHub | Official | Organizations / Repositories | UI, API, CLI |
| Google Workspace | Official | Domains | UI, API, CLI |
| LLM | Official | Models | CLI |
| M365 | Official | Tenants | UI, API, CLI |
| MongoDB Atlas | Official | Organizations | UI, API, CLI |
| Okta | Official | Organizations | CLI |
| Vercel | Official | Teams / Projects | UI, API, CLI |
Kubernetes
| Provider | Support | Audit Scope/Entities | Interface |
|---|---|---|---|
| Kubernetes | Official | Clusters | UI, API, CLI |
Containers
| Provider | Support | Audit Scope/Entities | Interface |
|---|---|---|---|
| Image | Official | Container Images / Registries | CLI, API |
Custom Providers (Prowler Cloud Enterprise Only)
| Provider | Support | Audit Scope/Entities | Interface |
|---|---|---|---|
| VMware/Broadcom VCF | Official | Infrastructure | CLI |
Where to go next?
User Guide
Detailed instructions on how to use Prowler.
Development Guide
Interested in contributing to Prowler?