Overview
The Bulk Provider Provisioning tool automates the creation of cloud providers in Prowler App or Prowler Cloud by:- Reading provider configurations from YAML files
- Creating providers with appropriate authentication credentials
- Testing connections to verify successful authentication
- Processing multiple providers concurrently for efficiency
Prerequisites
Requirements
- Python 3.7 or higher
- Prowler API key (from Prowler Cloud or self-hosted Prowler App)
- For self-hosted Prowler App, remember to point to your API base URL
- Learn how to create API keys: Prowler App API Keys
- Authentication credentials for target cloud providers
Installation
Clone the repository and install the required dependencies:Authentication Setup
Configure your Prowler API key:- Log in to Prowler Cloud or Prowler App
- Click Profile → Account
- Click Create API Key
- Provide a descriptive name and optionally set an expiration date
- Copy the generated API key (it will only be shown once)
Configuration File Structure
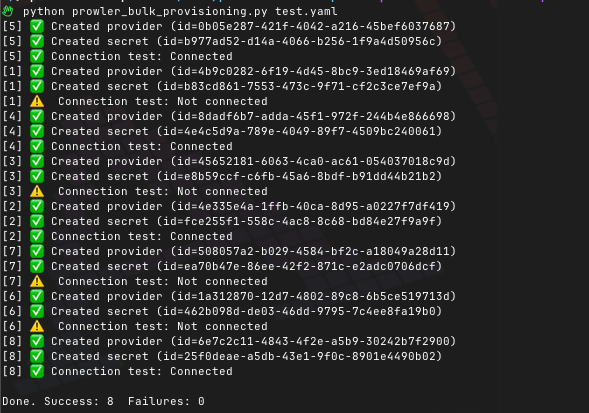
Create a YAML file listing your cloud providers and credentials:Running the Bulk Provisioning Tool
Basic Usage
To provision all providers from your configuration file:Dry Run Mode
Test your configuration without making API calls:Skip Connection Testing
To provision providers without testing connections:Test Existing Providers Only
To verify connections for already provisioned providers:Provider-Specific Configuration
AWS Provider Configuration
Using IAM Role (Recommended)
Using Access Keys
Azure Provider Configuration
GCP Provider Configuration
Using Service Account JSON
Using OAuth2 Credentials
Kubernetes Provider Configuration
Microsoft 365 Provider Configuration
GitHub Provider Configuration
Using Personal Access Token
Using GitHub App
Advanced Configuration
Concurrent Processing
Adjust the number of concurrent provider creations:Custom API Endpoints
For self-hosted Prowler App installations:Timeout Configuration
Set custom timeout for API requests:Bulk Provider Management
Deleting Multiple Providers
To remove all providers from your Prowler account:Configuration File Format
The tool uses YAML format for provider configuration files. Each provider entry requires:provider: The cloud provider type (aws, azure, gcp, kubernetes, m365, github)uid: Unique identifier for the provider (account ID, subscription ID, project ID, etc.)alias: A friendly name for the providerauth_method: Authentication method to usecredentials: Authentication credentials specific to the provider and method