This feature is exclusively available in Prowler Cloud. For CLI-based multi-account scanning, see AWS Organizations in Prowler CLI.
Overview
Individual Accounts vs Organizations
| Approach | Best for | How it works |
|---|---|---|
| Individual accounts | A few AWS accounts | Connect each account one by one with its own IAM role. |
| AWS Organizations | 10+ accounts, or any org-managed environment | Connect once to your management account, discover all member accounts automatically, and scan them in bulk. |
How it works
Before using the AWS Organizations wizard, you need to deploy two IAM roles in your AWS environment. The onboarding follows this sequence:
Key Concepts
What is an External ID?
An External ID is a security token that Prowler generates unique to your tenant. When Prowler assumes the IAM role in your AWS account, it presents this External ID to prove its identity. This prevents the confused deputy problem — a scenario where an unauthorized party could trick AWS into granting access to your account. By requiring the External ID, only your specific Prowler tenant can assume the role. You don’t need to create the External ID yourself — Prowler generates it automatically and displays it in the wizard for you to copy.Two Roles Architecture
Prowler requires two separate IAM roles deployed in different places, each with a distinct purpose:| Role | Where it lives | What it does | How to deploy it |
|---|---|---|---|
| ProwlerScan (management account) | Your management (root) account only | Discovers the Organization structure and scans the management account. Has additional Organizations discovery permissions. | Via Quick Create link or manually in the IAM Console (Step 1). Cannot be deployed via StackSet. |
| ProwlerScan (member accounts) | Every member account | Scans the account for security findings. | Via CloudFormation StackSet (Step 2). Automated across all accounts. |

Same name, different permissions. Both roles are named
ProwlerScan — Prowler expects a consistent role name across all accounts. The management account role has the same scanning permissions as member accounts, plus additional Organizations discovery permissions (see Step 1 for the full list).What is a CloudFormation StackSet?
A CloudFormation StackSet lets you deploy the same CloudFormation template across multiple AWS accounts in a single operation. Prowler uses a StackSet to deploy the ProwlerScan IAM role into every member account of your organization, so you don’t have to create the role manually in each account.Prerequisites
Prowler Cloud Account
You need an active Prowler Cloud account. Each AWS account you connect will count as a provider in your subscription. See Billing Impact for details.AWS Organization Enabled
Your AWS environment must have AWS Organizations enabled. You will need access to the management account (or a delegated administrator account) to provide the Organization ID and IAM Role ARN.Step 1: Create the Management Account Role
The first role you need to create is the management account role. This role allows Prowler to discover your Organization structure — listing accounts, OUs, and hierarchy.The role must be named
ProwlerScan — the same name as the role deployed to member accounts via StackSet. Prowler expects a consistent role name across all accounts in the Organization. If you use a different name, connection tests and scans will fail for the management account.Option A: Quick Create Link (Fastest)
The Prowler wizard provides a one-click link that opens the AWS Console with the CloudFormation template pre-configured. This creates a CloudFormation Stack (not a StackSet) that deploys the ProwlerScan role with Organizations permissions enabled in your management account.- Click Open Quick Create Stack in AWS Console → or use the Create Stack in Management Account button in the Prowler wizard (which also pre-fills the ExternalId).
- Enter the ExternalId parameter if not pre-filled.
- Check “I acknowledge that AWS CloudFormation might create IAM resources with custom names” and click Create stack.
- Wait for the stack to reach CREATE_COMPLETE status.
Option B: Create the Role Manually
- Sign in to the AWS IAM Console in your management account.
- Go to Roles > Create role and select Custom trust policy.
- Paste the following trust policy. This allows Prowler Cloud to assume the role using your tenant’s External ID (you will get this from the Prowler wizard in Step 3):
<YOUR_EXTERNAL_ID> with the External ID shown in the Prowler wizard.
-
Attach the following AWS managed policies:
- SecurityAudit
- ViewOnlyAccess
- Create an additional inline policy with the following permissions. These are specific to the management account and allow Prowler to discover your Organization structure:
- Name the role
ProwlerScanand click Create role. Take note of the Role ARN — you will need it in the Prowler wizard.
arn:aws:iam::<account-id>:role/ProwlerScan
If you just created the role, it may take up to 60 seconds for AWS to propagate it. If you get an error in the Prowler wizard, wait a moment and try again.
Step 2: Deploy the CloudFormation StackSet
After creating the management account role, the next step is to deploy the ProwlerScan role to your member accounts using a CloudFormation StackSet. This is the recommended method for consistent, scalable deployment across your entire organization. The StackSet uses service-managed permissions, which means AWS Organizations handles the cross-account deployment automatically — you don’t need to create execution roles manually in each account. The StackSet deploys the ProwlerScan IAM role in every target member account, enabling Prowler to assume that role for cross-account scanning.Trusted access required: CloudFormation StackSets must have trusted access enabled in your management account. Verify this in the AWS Console under AWS Organizations > Settings > Trusted access for AWS CloudFormation StackSets.
- Click the link above or navigate to CloudFormation > StackSets > Create StackSet in your management account.
- Choose Service-managed permissions.
- Select Amazon S3 URL as the template source and paste the following URL:
- Set the ExternalId parameter to the External ID shown in the Prowler wizard.
- Choose your deployment targets (entire organization or specific OUs).
- Select the AWS regions where you want the role deployed.
- Click Create StackSet.
Verify StackSet Deployment
After deploying, verify that all stack instances completed successfully:- In the CloudFormation Console, go to StackSets and select your Prowler StackSet.
- Click the Stack instances tab.
- Confirm that all instances show Status: CURRENT and Stack status: CREATE_COMPLETE.
Prefer Terraform? You can deploy the ProwlerScan role using Terraform instead. See the StackSets deployment guide for the Terraform module.
Key Considerations
- Service-managed permissions: Always select Service-managed permissions when creating the StackSet. This lets AWS Organizations manage the deployment automatically across current and future member accounts.
- Least privilege: The ProwlerScan role deployed by the StackSet uses
SecurityAuditandViewOnlyAccess— AWS managed policies that grant read-only access — plus a small set of additional read-only permissions for services not covered by those policies. See the CloudFormation template for the full list. Prowler does not make any changes to your accounts. - New accounts: When you add new accounts to your AWS Organization, the StackSet automatically deploys the ProwlerScan role to them if you targeted the organization root or the relevant OU. Combined with Prowler’s 6-hour automatic sync, new accounts are onboarded end-to-end without manual intervention.
- Management account: Organizational StackSets do not deploy to the management account itself. If you want to scan the management account, you need to create the ProwlerScan role there separately using a regular CloudFormation Stack.
Step 3: Start the Organization Wizard
Now that both roles are deployed — the management account role (Step 1) and the ProwlerScan role in member accounts (Step 2) — you can start the Prowler wizard.Open the Wizard
- Navigate to Providers and click Add Provider.
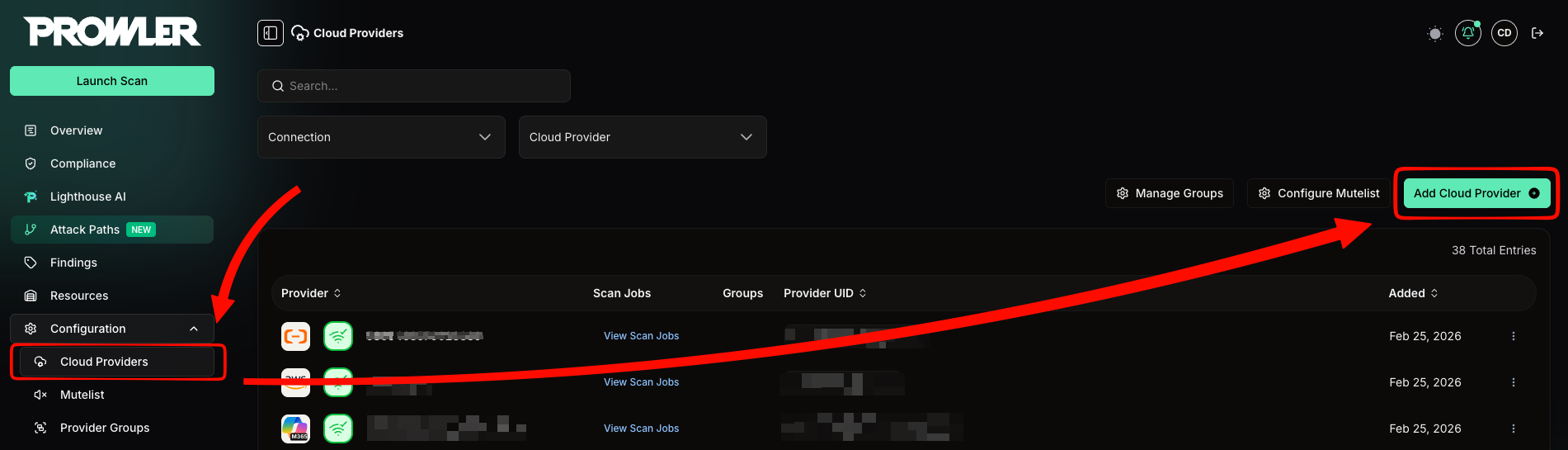
- Select Amazon Web Services as the provider.
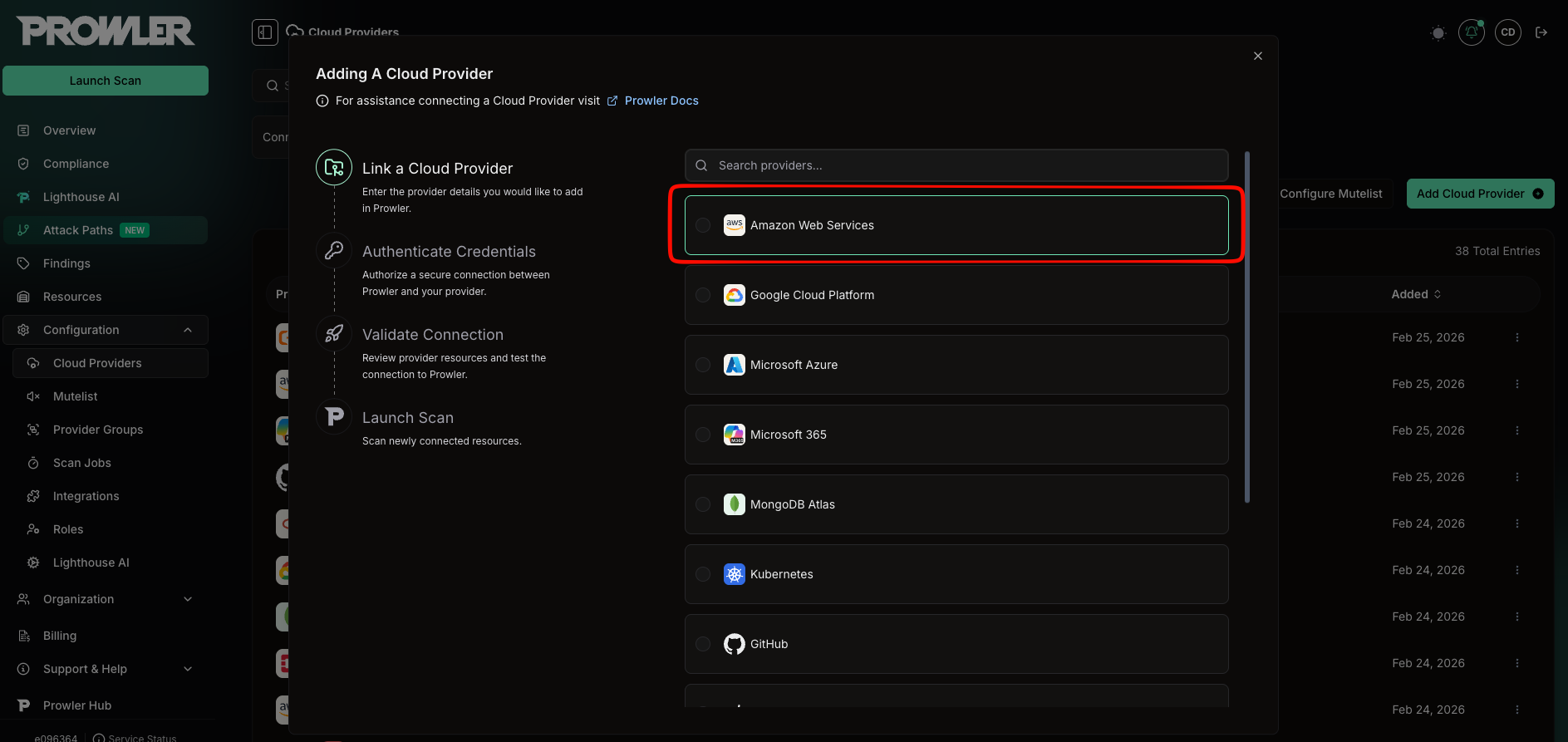
- Choose Add Multiple Accounts With AWS Organizations.
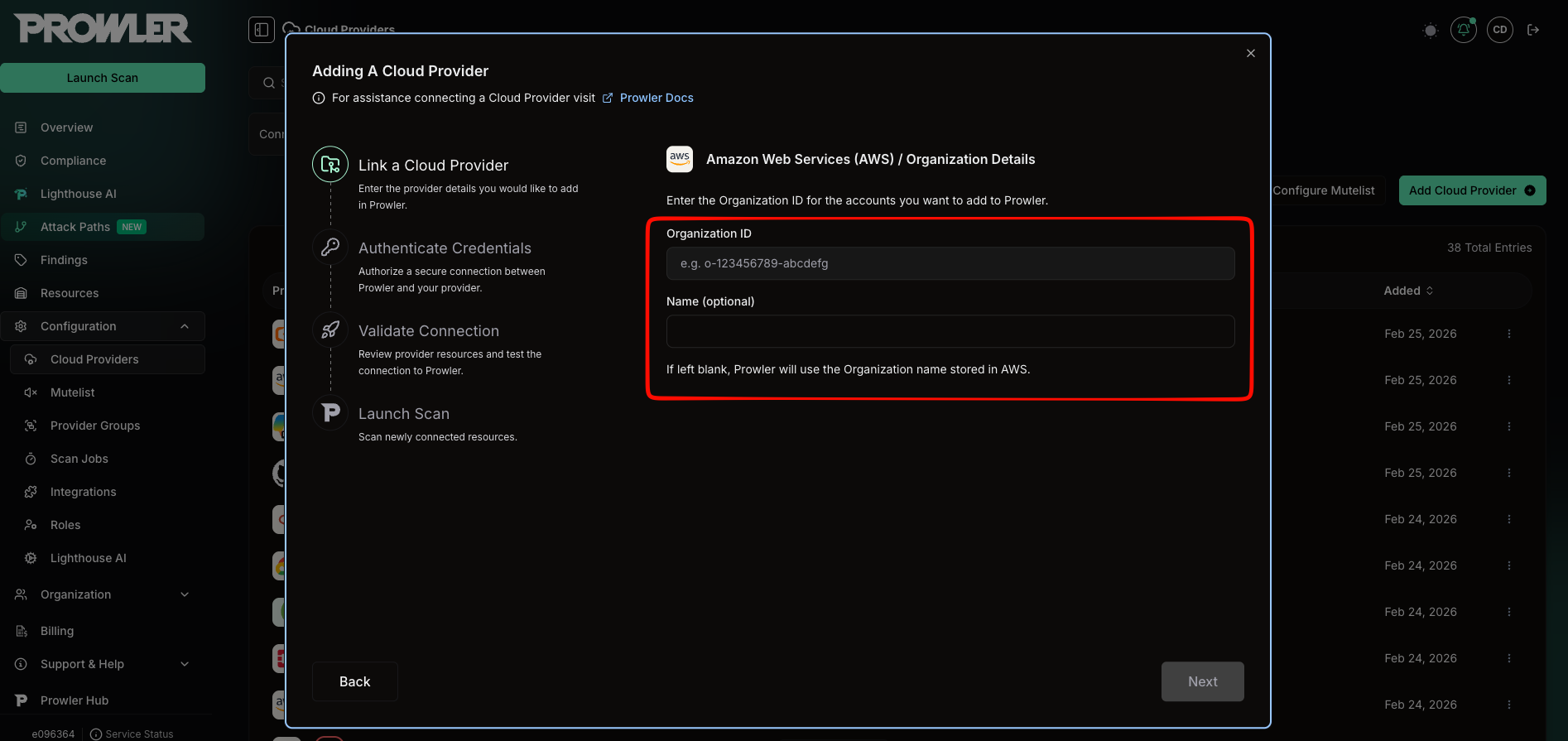
Enter Organization Details
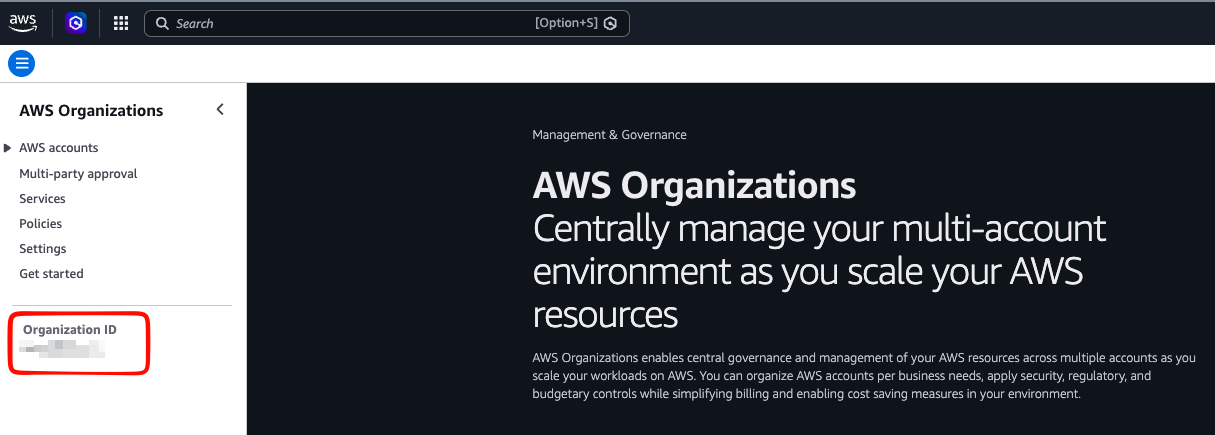
- Organization ID: Your AWS Organization identifier, found in the AWS Organizations Console. It follows the format
o-followed by 10–32 lowercase alphanumeric characters (e.g.,o-abc123def4). You can find it in the left sidebar of the AWS Organizations console:
- Name (optional): A display name for the organization. If left blank, Prowler uses the name stored in AWS.
Step 4: Authenticate with Your Management Account
The wizard’s Authentication Details page guides you through three actions: deploying the roles in AWS, entering the management account Role ARN, and confirming the deployment.External ID
The wizard displays a Prowler External ID at the top — auto-generated and unique to your tenant. Click the copy icon to copy it. You will need this External ID for both the management account Stack and the member accounts StackSet.Deploy the Roles
The wizard provides two deployment actions:-
Create Stack in Management Account — opens a Quick Create link that deploys the ProwlerScan role with
EnableOrganizations=truein your management account (Step 1). The External ID is pre-filled. - Open StackSets Console — links to the CloudFormation StackSets console where you create a StackSet for member accounts (Step 2). Copy the template URL shown in the wizard and paste the External ID manually.
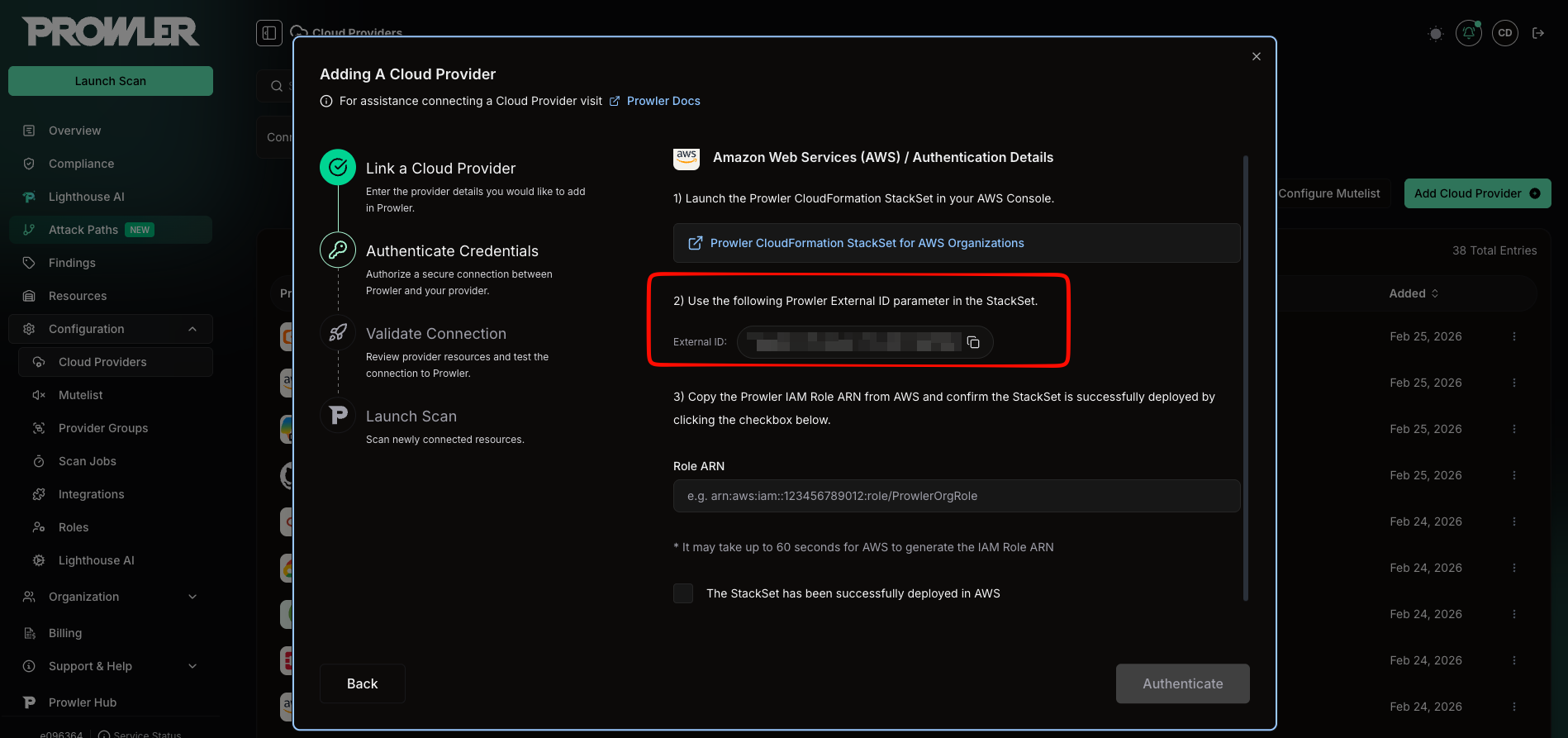
Enter the Management Account Role ARN
Paste the Role ARN of the management account role you created in Step 1 into the Management Account Role ARN field. The ARN follows this format:arn:aws:iam::123456789012:role/ProwlerScan
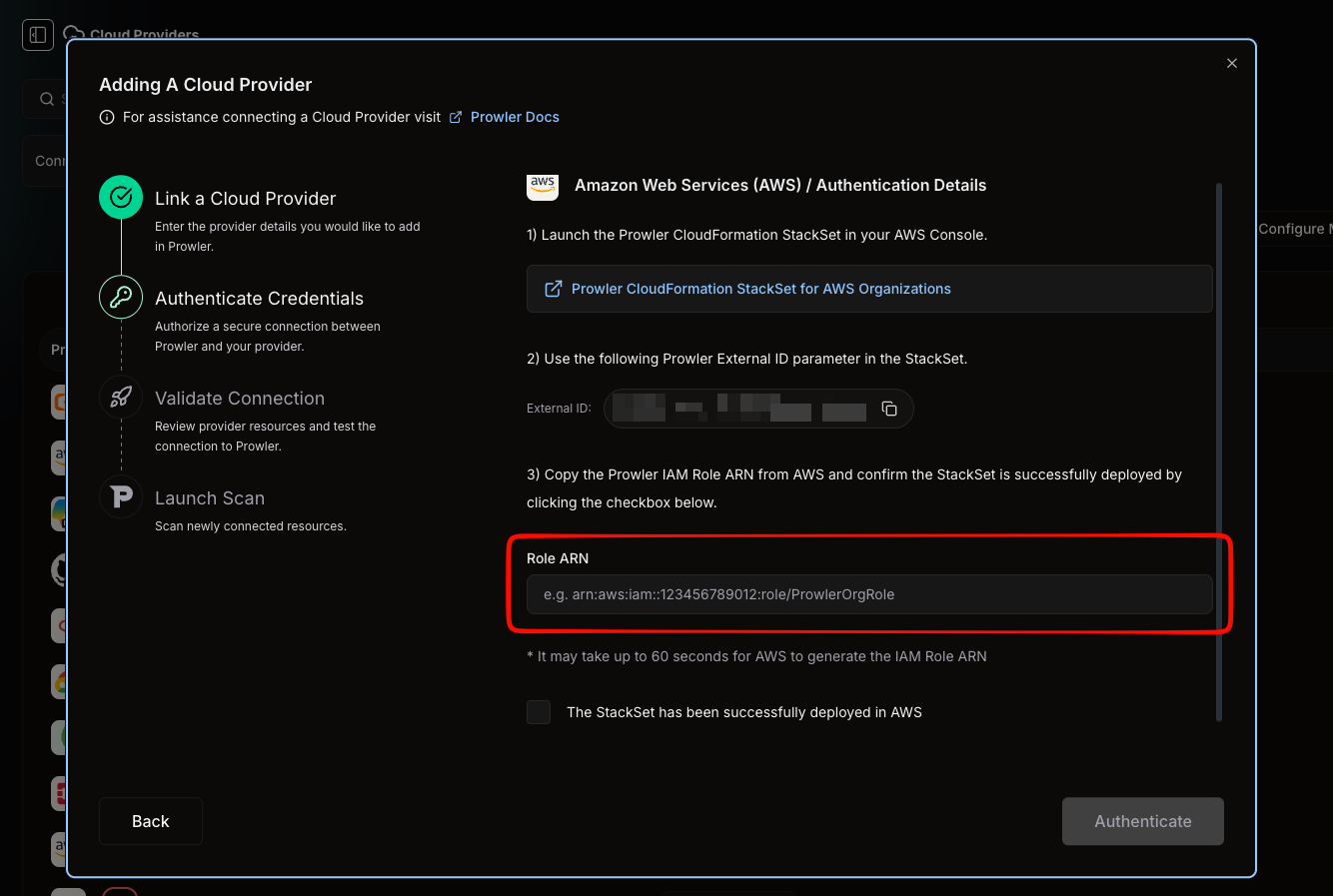
Confirm and Discover
- Check the box: “The Stack and StackSet have been successfully deployed in AWS”.
- Click Authenticate.
- Prowler creates the organization resource and stores your credentials securely.
- An asynchronous discovery is triggered to query your AWS Organization structure.
- You will see a “Gathering AWS Accounts…” spinner — this typically takes 30 seconds to 2 minutes depending on your organization size.
Step 5: Select Accounts to Scan
Understanding the Tree View
Once discovery completes, the wizard displays a hierarchical tree view of your Organization: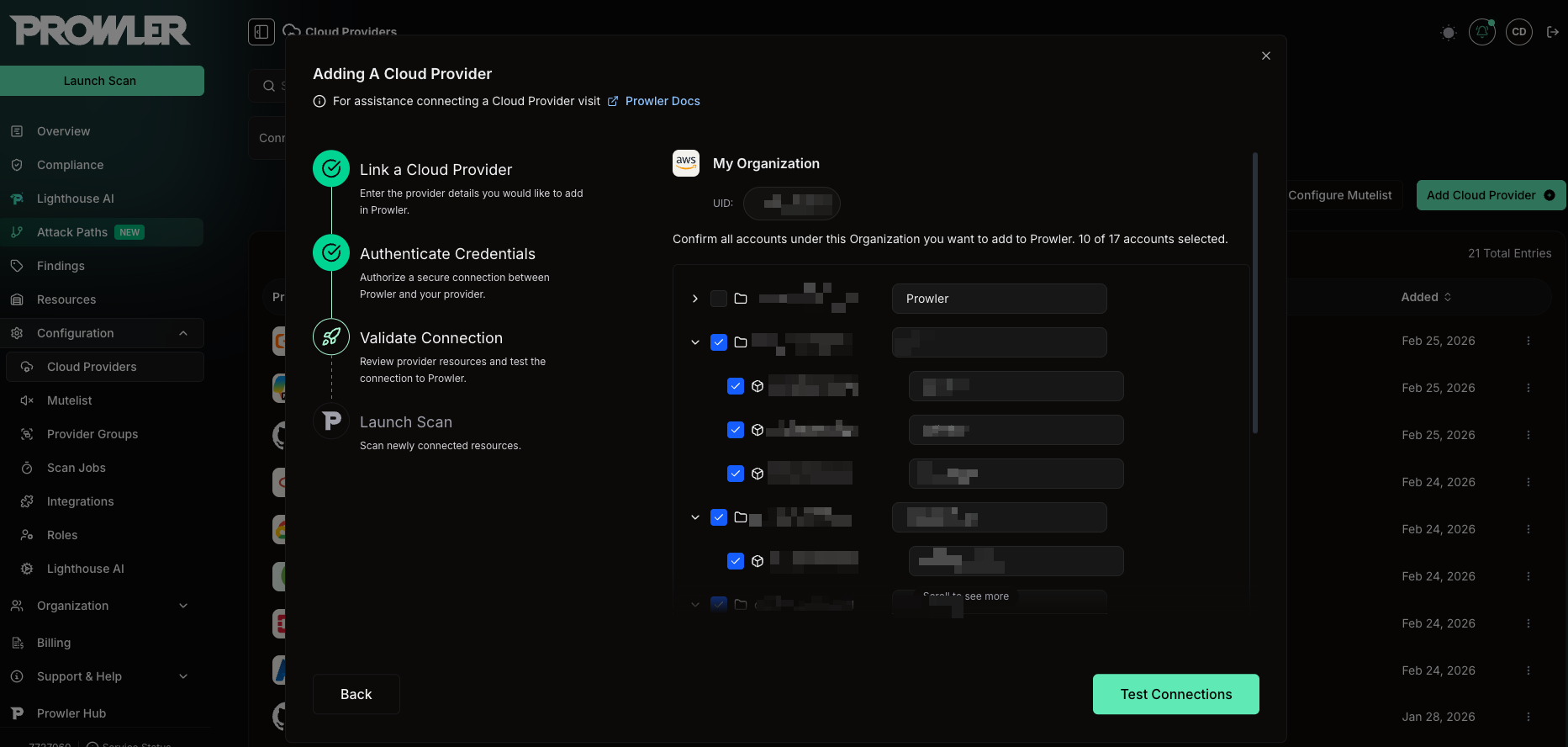
- The tree supports up to 5 levels of nesting (Root > OUs > Sub-OUs > Accounts).
- Selecting an OU automatically selects all accounts within it.
- Individual overrides: deselect specific accounts even if the parent OU is selected.
- The header shows “X of Y accounts selected” to track your selection.
Account Statuses
Only ACTIVE accounts can be selected for scanning:| Status | Selectable? | Description |
|---|---|---|
| ACTIVE | Yes | Account is active and operational. |
| SUSPENDED | No | Account is suspended by AWS. |
| PENDING_CLOSURE | No | Account is being closed. |
| CLOSED | No | Account has been closed. |
Your existing data is safe. If an AWS account is already connected to Prowler as an individual provider, it will appear in the tree with a checkmark indicator.When you proceed:
- The existing provider is linked to the organization — it is not duplicated.
- All your historical scan data and findings are preserved — nothing is overwritten.
- There is no additional billing — the existing provider is reused.
Custom Aliases
You can edit the display name for each account before connecting. This alias is only used in Prowler — it does not affect your AWS account name.Blocked Accounts
Some accounts may appear as blocked (grayed out, not selectable). This happens when:- The account is already linked to a different organization in Prowler (
linked_to_other_organization).
Step 6: Test Connections
How Connection Testing Works
Click Test Connections to verify that Prowler can assume the ProwlerScan role in each selected member account.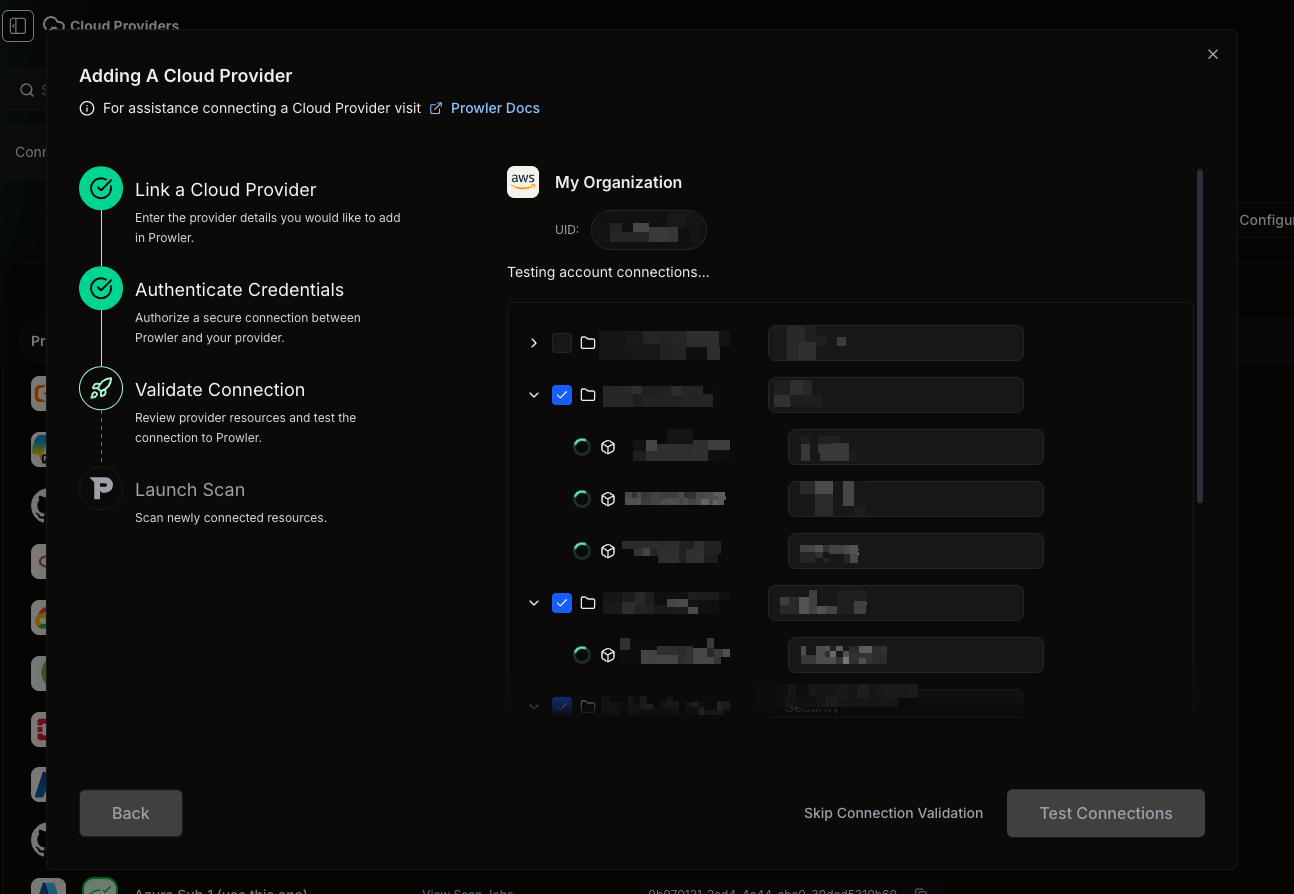
- Each account shows a real-time status indicator:
- Spinner — test in progress
- Green checkmark (✓) — connection successful
- Red icon (✗) — connection failed (hover to see the error)
All Tests Pass
If every account connects successfully, you automatically advance to the next step.Some Tests Fail
An error banner appears: “There was a problem connecting to some accounts.” You have two options: a) Fix and retry:- Go to the AWS Console and verify the StackSet deployed to the failing accounts.
- Check that the External ID in the StackSet matches the one shown in Prowler.
- Return to Prowler and click Test Connections — only the failed accounts are re-tested (smart retry). Accounts that already passed are not tested again.

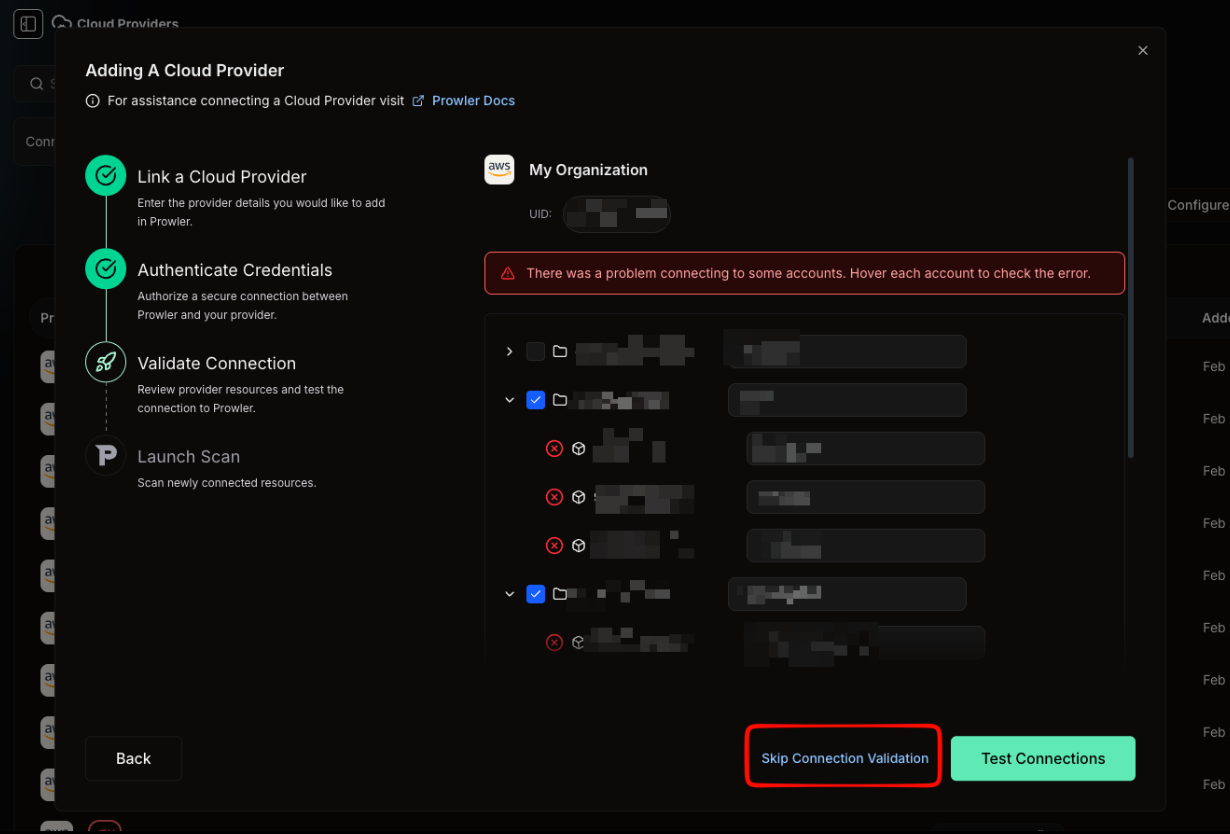
Skip Connection Validation is only available when at least one account connected successfully.
All Tests Fail
If no accounts connected successfully, you cannot proceed:“No accounts connected successfully. Fix the connection errors and retry before launching scans.”You must fix the underlying connection issues before continuing. See Updating Credentials below.
Updating Credentials
If connection tests fail, here’s how to fix common issues:- Open the CloudFormation Console and check that your StackSet instances show CREATE_COMPLETE for the failing accounts. If not, update the StackSet to include the missing OUs.
- Compare the ExternalId parameter in your StackSet with the External ID displayed in the Prowler wizard. They must match exactly.
- After fixing the issue in AWS, return to Prowler and click Test Connections. Only the previously failed accounts will be re-tested.
Step 7: Launch Scans
Choose Scan Schedule
| Schedule Option | Description |
|---|---|
| Scan Daily (every 24 hours) | Creates a recurring daily scan for all connected accounts (default). |
| Run a single scan (no recurring schedule) | Launches a one-time scan. |
Launch
Click Launch scan. A toast notification confirms: “Scan Launched — Daily scan scheduled for X accounts” with a link to the Scans page. You will be redirected to the Providers page. Scans are only launched for accounts that are accessible (passed connection testing) and were selected.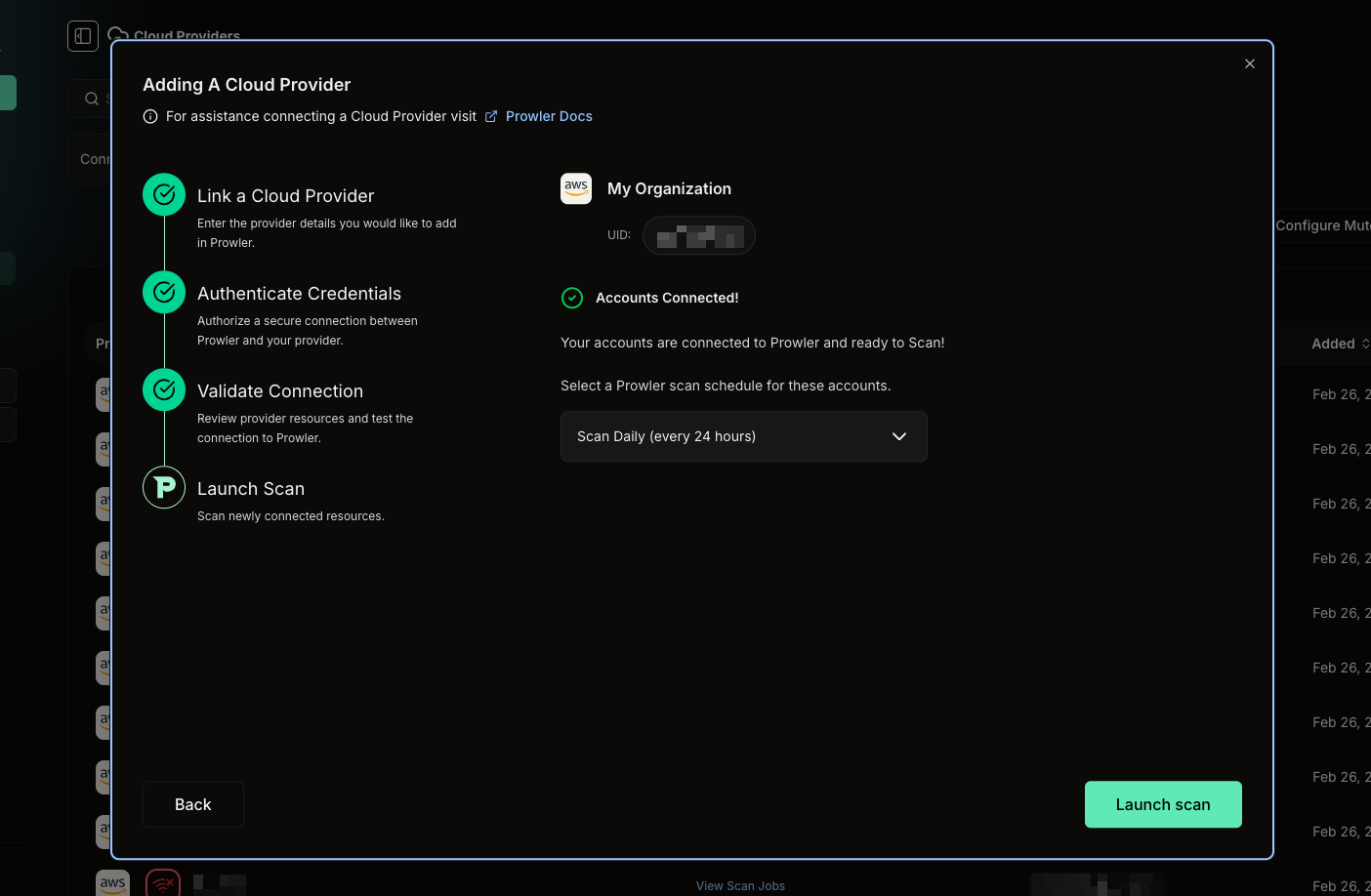
What Happens Next
- Scans appear in the Scans page as they start and complete.
- Results populate the Overview and Findings pages.
- Prowler runs an automatic sync every 6 hours to detect new accounts added to your Organization or accounts that have been removed. New accounts are onboarded automatically based on the parent OU configuration.
Billing Impact
Each AWS account you connect through the Organizations wizard counts as one provider in your Prowler Cloud subscription.- Already-connected accounts: if an account was already linked as a provider, adding it to the organization does not incur additional billing. The existing provider is reused.
- Large organizations: connecting a 500-account organization will result in up to 500 providers on your subscription. Review your plan limits before proceeding.
- Deleted providers: if you later remove an account, the deleted provider no longer counts toward your subscription.
Troubleshooting
Invalid AWS Organization ID
“Must be a valid AWS Organization ID”- Verify the Organization ID format:
o-followed by 10–32 lowercase alphanumeric characters (e.g.,o-abc123def4) - Copy it directly from the AWS Organizations Console to avoid typos
Invalid IAM Role ARN
“Must be a valid IAM Role ARN”- Verify the ARN format:
arn:aws:iam::<12-digit-account-id>:role/<role-name> - Copy the ARN directly from the IAM Console in your management account
Authentication Failed
“Authentication failed. Please verify the StackSet deployment and Role ARN”- Verify the management account role exists and was created in Step 1
- Confirm the trust policy includes the correct External ID from the wizard
- Check the role has all Organizations discovery permissions listed in Step 1
- Double-check the Role ARN format and account ID for typos
Authentication Timed Out
“Authentication timed out”- Retry the authentication step — the second attempt often succeeds
- Check for AWS API rate limiting on the Organizations service
- For very large organizations (500+ accounts), allow extra time for discovery
Connection Test Fails for All Accounts
No accounts pass the connection test.- Verify the CloudFormation StackSet was deployed — complete Step 2 and wait for stack instances to reach CREATE_COMPLETE
- Check that the ExternalId parameter in the StackSet matches the External ID shown in the Prowler wizard
- If your accounts use IP-based IAM policies, allow Prowler Cloud public IPs
Connection Test Fails for Some Accounts
Some accounts show a red icon while others pass.- Expand the StackSet deployment to include the OUs containing the failing accounts
- Suspended accounts cannot be scanned — deselect them and proceed
- Ensure the STS regional endpoint is enabled in the account’s region
- After fixing, click Test Connections — only the failed accounts will be re-tested
No Accounts Connected Successfully
“No accounts connected successfully. Fix the connection errors and retry before launching scans.”- Hover over the red icon on each account to see the specific error
- Fix the underlying issues using the guidance above
- Click Test Connections to retry
Failed to Apply Discovery
“Failed to apply discovery”- Check the
blocked_reasonsfield for any blocked accounts - Retry the operation
- If the error persists, contact Prowler Support
What’s Next
Prowler Cloud
Full guide to using Prowler Cloud features.
AWS Organizations (CLI)
CLI-based Organizations scanning and StackSet deployment with Terraform.
Bulk Provider Provisioning
Script-based bulk provisioning for advanced automation.